Cybersecurity Best Practices for Ruby on Rails Developers
Reading time: ~ 4 minutes

Cybersecurity Best practices
Everyone deserves to be safe online, so it's important that we're aware of cybersecurity best practices. This way, we can make smart decisions for our internal teams and clients. It's also a good idea to have a plan of action in case of a bug or security breach, and because October is Cybersecurity Awareness Month, we wanted to share some helpful tips with you.
Risks in Having Poor Cybersecurity Management
As you likely already know, cybersecurity breaches can cause data loss, productivity loss, reputation damage, lawsuits, financial challenges, and major trust issues between a business and its customers. If you've ever had one of your personal accounts hacked, you know the massive headache it can cause. That's why when we're working on the back end of an application, we want to get ahead of security issues before they become a problem. Companies gain efficiency, trust, and substantial cost savings by combining a suite of cybersecurity and compliance services into one managed service.
Cybersecurity Tools for Your Internal Team
We use and recommend to all of our clients that they know cybersecurity best practices and specific measures to protect their sensitive data and devices. These include some of the following:
- Antivirus software- Finds viruses and other harmful malware, like ransomware, worms, spyware, adware, and Trojans.
- Our team currently uses ClamAV to scan our development machines
- Encryption tools- Protect information by scrambling text, making it unreadable by unauthorized users
- Firewall tools- Monitor network traffic and permit or block data packets based on a set of cybersecurity rules
- Network intrusion detection- Monitor network and system traffic for unusual or suspicious activity and alert the admin if a potential threat is detected
- Network security monitoring tools- Used to analyze network data and detect network-based threats.
- Penetration testing- Tests that simulate an attack on a computer in order to evaluate the security of that system
- Web vulnerability scanning tools- Scans web apps to identify security vulnerabilities
Some other tools we use internally and recommend to clients
One Time Secret: When we request account credentials from a client, or vice versa, we must share the credentials in a secure way. One Time Secret creates a secret link that only works once and disappears forever.
1Password: This is the easiest way to store and use strong passwords. By adding the extension on a web browser, users can log in to any website and fill out forms securely with a single click. 1Password's end-to-end encryption gives us and our clients peace of mind that every precaution is taken to protect sensitive information.
MFA's: Multi-factor Authentication (MFA) requires users to provide two or more verification factors to gain access to an application or online account.
You might be familiar with Authy, a two-factor authentication app that encrypts all backups, ensuring your data is safe from hackers. In addition, if a user loses their device, cloud-based backups enable them to access their credentials safely on another device.
Encrypted laptop hard drives can be done via your operating system settings. For example, all of our employees on macOS enable this via FileVault.
Cybersecurity Best Practices for Ruby on Rails Developers
One of the simplest things developers should do to protect their apps is to keep them up-to-date with the latest security patches.
Every application has dependencies, which can have security holes, which opens the app up to security vulnerabilities. They're also challenging to detect, so if there's a bug somewhere within your app, how will you find it? Or even know that it exists? You could subscribe to every mailing list related to security announcements or follow the dev work of every library you depend on for every application. Or you could automate it, saving a lot of time.
For Ruby apps, you can use Bundler-Audit or Bundler to run a simple check. The tool will look for any known security vulnerabilities for the specific versions of all your Rails application's dependencies and provide your team with a list of recommended versions to upgrade to, eliminating the time it would take to figure this all out manually. We recommend having this be an automated process run by your favorite Continuous Integration service (e.g., GitHub Actions, CircleCI, etc.).
Brakeman is a static analysis tool that scans for known insecure patterns, vulnerabilities, and configurations in the code base. Unlike many web security scanners, Brakeman scans the source code itself, meaning it can be run at any stage of development, and you don't need to set up your whole application stack to use it.
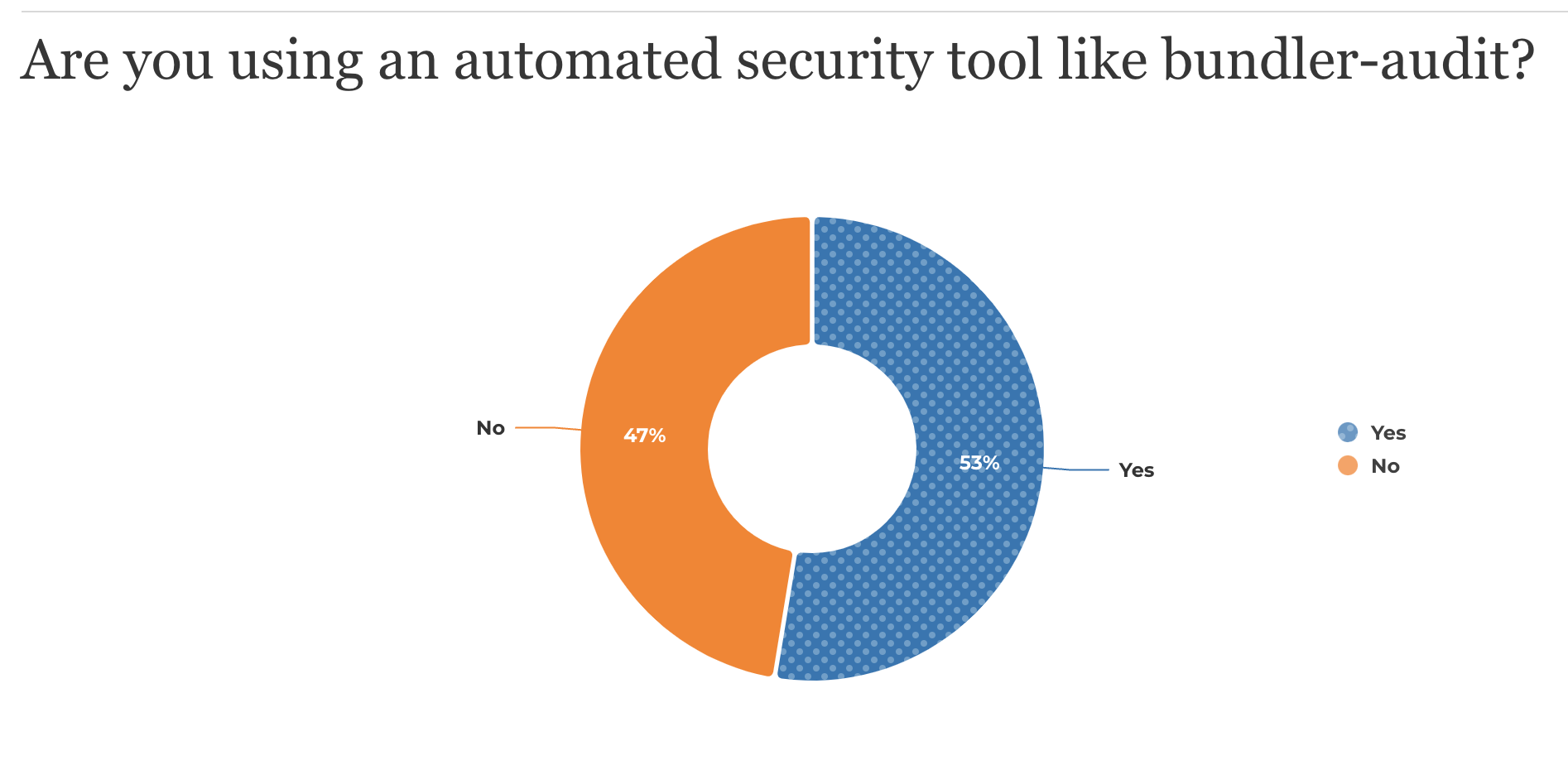
In our 2022 Ruby on Rails Community Survey, 53% of respondents said they were using an automated security tool like the ones mentioned above.
OAuth2 is an open standard for authorization that provides applications with "secure delegated access" that anyone can implement. It's an authorization protocol, not an authentication protocol, so it's designed to grant access to a set of resources, like remote APIs or a user's data. The Ruby on Rails community can lean on Rubygems like Devise or OmniAuth to assist with these integrations.
Working Through Risks and Vulnerabilities
We recommend that you work with one scanner/audit service at a time. Once you've run the tool and received your report, begin with the highest risks first, then filter the others and work backward. You might also find false positives for various reasons, which can be added to a separate list to filter out the noise.
After fixing an issue, test that your application still behaves as expected before deploying the change to production.
Now you can run these tools on every code change you commit, and you'll always know when your security standards need to be updated.
How Planet Argon Addresses Cybersecurity or Support Updates for Clients
Occasionally, a library that our clients' applications rely on will announce a new security vulnerability, putting the client's app and their users at risk. We address these urgent incidents in our contract agreements, confirming with the client that our team will work to fix the vulnerability as soon as possible. It's also important that we give the client an estimate of how long it should take to make the update.
Planet Argon’s Rails Support & Maintenance Services
Plenty of work goes into a Ruby on Rails web application beyond the initial launch. Our ongoing maintenance and support service keeps Ruby on Rails applications running at their best.
As part of our Rails Support & Maintenance Service, we help to make improvements and solve problems as they arise. This includes regular updates and bug fixes, which are key to an efficient web application.
Do you know someone who might benefit from this type of service? Send them our way- we'd love to chat with them!
In Closing
Knowing cybersecurity best practices and implementing them are two different things. So let's continue making the online space a safe place by keeping our apps and websites as secure as possible.
